Website spoofing. Sounds funny doesn’t it?
Although we all love a good spoof when it comes to the movies, website spoofing, unfortunately, isn’t very funny.
The practice of spoofing websites, sometimes referred to as domain spoofing, can be used for a variety of malicious purposes. And for a developer or coder with fairly basic knowledge, it’s pretty easy to do.
What does website spoofing mean?
A spoofed website is a site that has been fraudulently copied and is also referred to as domain spoofing. This can be done by creating a website that looks similar to the original and using a fake domain name.
Domain spoofing can also be done using a genuine URL with a falsified slug. So, the domain URL will be correct, for example, Forbes.com. But the slug will go to a non-existing page, for example, /buy-best-coffee-beans.
This is a method used by 404Bot, an active ad fraud network, to generate fake ad impressions using genuine URLs.
With the domain spoofed, fraudsters can then force a redirect from the original URL or find ways to drive traffic using bots.
These types of websites can often look exactly the same as the genuine article, with the same content, logo, font, and contact information. However, the name or some other element might be different, for example, f0rbes.com, forbes.xyz, or forbes-online.net.
Website spoofing examples
As an example, I looked up f0rbes.com and it landed on this hot mess of a spoofed website. The URL, as you’ll notice, is totally different from the one I entered and the site itself is trying to copy the UK’s Mirror.co.uk news site.
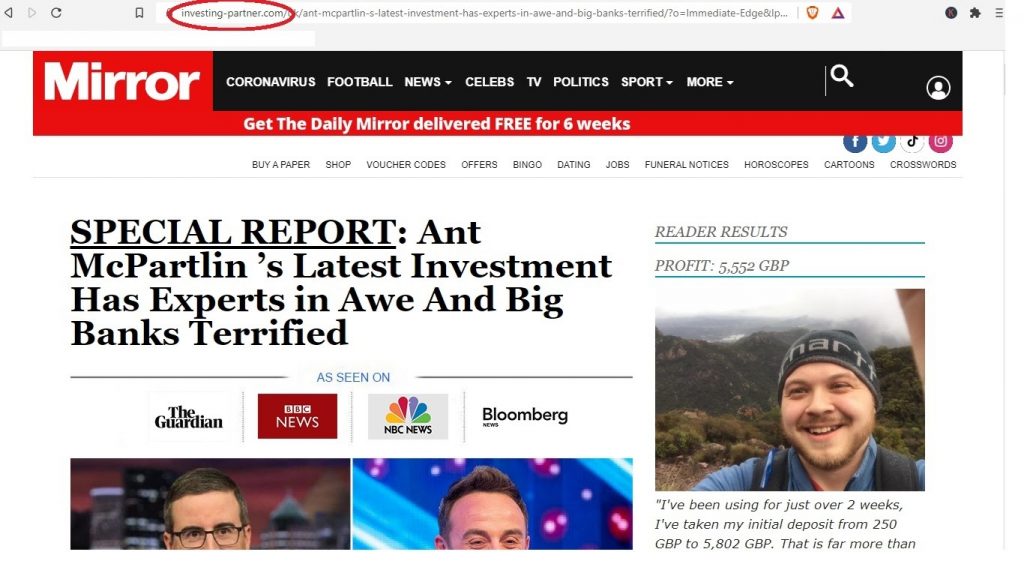
The content is trying to sell some sort of shady crypto investment, so is basically a phishing scam.
Refreshing the site actually brings up another bogus news article, this time from a spoofed BBC page. Again, it’s about Bitcoin and is asking for personal details and payment information.
Entering the actual domain from the browser results in a 404 page. So clearly this is a scam website.
What is a website or domain spoofing used for?
Of course, spoofed websites are used for a wide range of fraudulent purposes. These include:
- Phishing or stealing personal information
- Stealing data or bypassing security
- Hijacking traffic for fraud or cyber attacks
- Making a fraudulent website appear genuine
- Spreading malware or spyware
- Committing ad fraud by forcing fake ad views
Spoofing attacks are usually used for data breaches, or even as a precursor to DDoS or ransomware attacks.
One of the most common ways to use spoofed websites is for phishing, usually by linking from within an SMS text message or email. The user then assumes that the website is a genuine article and inputs their login details or other sensitive information.
However, as you can see above, website spoofing has a wide variety of applications.
Ad fraud, a popular and lucrative cybercrime, often uses spoofed websites. This form of click fraud sees fraudulent publishers generate spoofed domains to host banner or video ads, and then use bot traffic to inflate the views and the ad payout.
A lot of ad fraud also comes from malware, such as the DrainerBot campaign. This sneaky bot worked in the background of apps on users’ devices as a malware install. It would generate views and impressions of video and banner ads on spoofed websites without the users’ knowledge.
Email spoofing
One aspect of domain spoofing is creating fake email addresses or email spoofing.
These are usually part of the phishing or scamming process, designed to get you to click and engage with the spoofed site. This practice is known as social engineering, where a scammer gains the trust of someone with the intent to defraud them.
Email spoofing can also happen after a data breach. For example, if your website has been hacked or experienced a DDoS attack, you might find your company emails being used to spam people.
This might be part of the hackers’ attempt to steal your user data, but can also be a sign of an ongoing security breach.
How can you spot spoofed or fake websites
As most forms of fraud related to spoofed websites come from your inbox or direct messaging, you should always pay attention to the link.
Even if a link appears to be from a reputable source, such as your bank, or other service provider, take a close look. Keep an eye out for odd spelling, unusual characters (such as Chinese font within English text), or anything that might look slightly out of place.
If in doubt, don’t click. Instead, enter the domain directly into your browser to check. If the message is flagging up an issue with your account, always contact customer service or log in without clicking the link in the message.
If you do find you have clicked what might be a spoofed domain link, avoid downloading or opening anything, or entering your details. And if you think your details have been compromised, let your service provider (bank, software service, etc) know.
Dodgy downloads
Malware or infected browser extensions can also be a source of spoofed domain traffic. These software infections can use your genuine human activity to perform clicks or activity on ads, download links, or domain URLs. This last one is a clever way that fraudsters use ‘genuine human visitors’ to inflate site traffic.
Ad fraud and website spoofing
Spotting if your PPC ads have been displayed on a spoofed site can be tricky.
Google does let you check your ad placements. And you can also customize where your ads appear if you’d prefer that they are only displayed on specific websites.
In general spotting an ad placement on a spoofed site can be like spotting a needle in a haystack. But as these kinds of fraud networks tend to use bots, there are other things to keep an eye out for.
Some of the giveaways are high volumes of traffic from a certain site, often accompanied by high bounce rates. You might also spot multiple clicks in a short amount of time, repeat clicks from the same IP address, or an increase in spam or abandoned shopping carts.
Using a click fraud protection service is the best way to prevent this kind of spoofing attack or bot traffic.
Blocking bots and fraud
Most of us are aware of the many security threats online. From phishing scams to bot traffic, businesses need fraud prevention more than ever.
For starters, business owners and managers should keep their workforce aware of the potential for security breaches, and how to avoid them. Awareness of email security, data protection, and communication practices can all help to reduce the chances of problems arising from a spoofing attack.
Blocking fraud bots on your website can also prevent issues from click fraud to carding.
Marketing professionals can protect their online ads using ClickCease. Sign up for a free trial to run an audit on your ads and see how much bot or VPN traffic you’re seeing.
